If you’re architecting cloud applications that accept file uploads from untrusted sources such as the Internet, one of the decisions you will need to make is how best to ensure you are not uploading files containing malware.
Typically, the files a cloud application needs to consume from the Internet will be Microsoft Office files, Adobe PDFs, images or archives. From the perspective of the cybercriminal, these all represent excellent carriers for concealed malware. While detection-based anti-virus scanners can find and stop some of the malware, ensuring uploaded files are totally threat-free requires a more radical approach.
The good news is there’s a way to ensure that file uploads are always threat-free that is easy to build directly into cloud applications. Rather than trying to detect malware, Deep Secure Threat Removal uses a process of transformation to ensure file uploads are always 100% threat-free.
It works by extracting the valid business information from files (either discarding or storing the originals), verifying the extracted information is well-structured and then building a brand new file to carry the information to its destination. This approach is recommended by the UK National Cyber Security Centre (NCSC). It is a game changer because it delivers 100% efficacy.
“Baked-in” Security Controls
Threat Removal is a cloud-native security solution, accessible via APIs and offered as a subscription-based service. It is built as a completely serverless solution, providing limitless scalability.
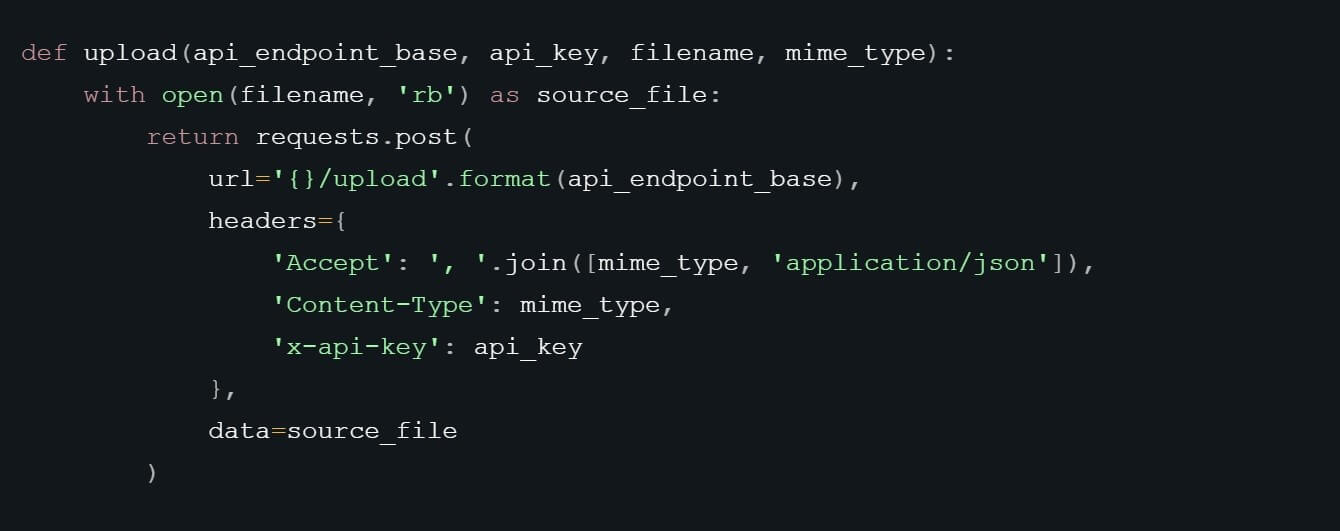
The APIs can be used by both Microsoft Azure and Amazon AWS development teams. From a developer perspective, it’s simple to “bake-in” Threat Removal security controls into the code by making cloud API calls. In the screen shot below for example, you can see how the developer is able to call out to the service and presents a file for sanitisation using just a few lines of code.
Developers can use different Threat Removal APIs depending on their particular project. To support this, Deep Secure offers an Async API for cloud and cross cloud workflows, an Instant API for simple direct request/response transactions and an S3 API for AWS native applications.
Building Cloud Applications that use Threat Removal
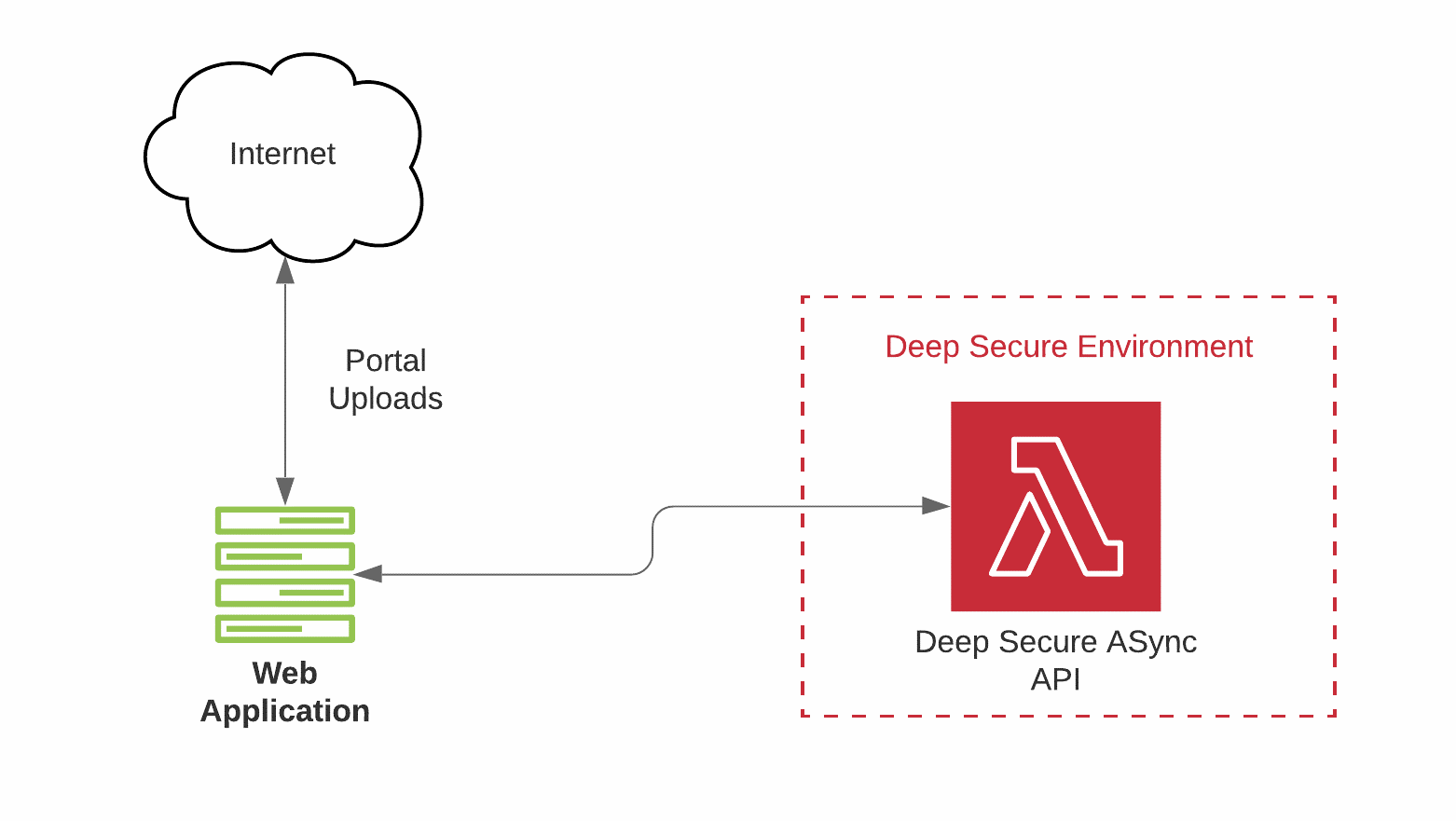
The example below is a high-level schematic showing how the Async API can be used in an application to prevent malicious file uploads. The Async API is a RESTFUL interface and is ideal for workflows that involve sending and receiving complex documents such as high-quality PDFs or marketing material and Microsoft Office documents.
Building Native AWS Applications that use Threat Removal
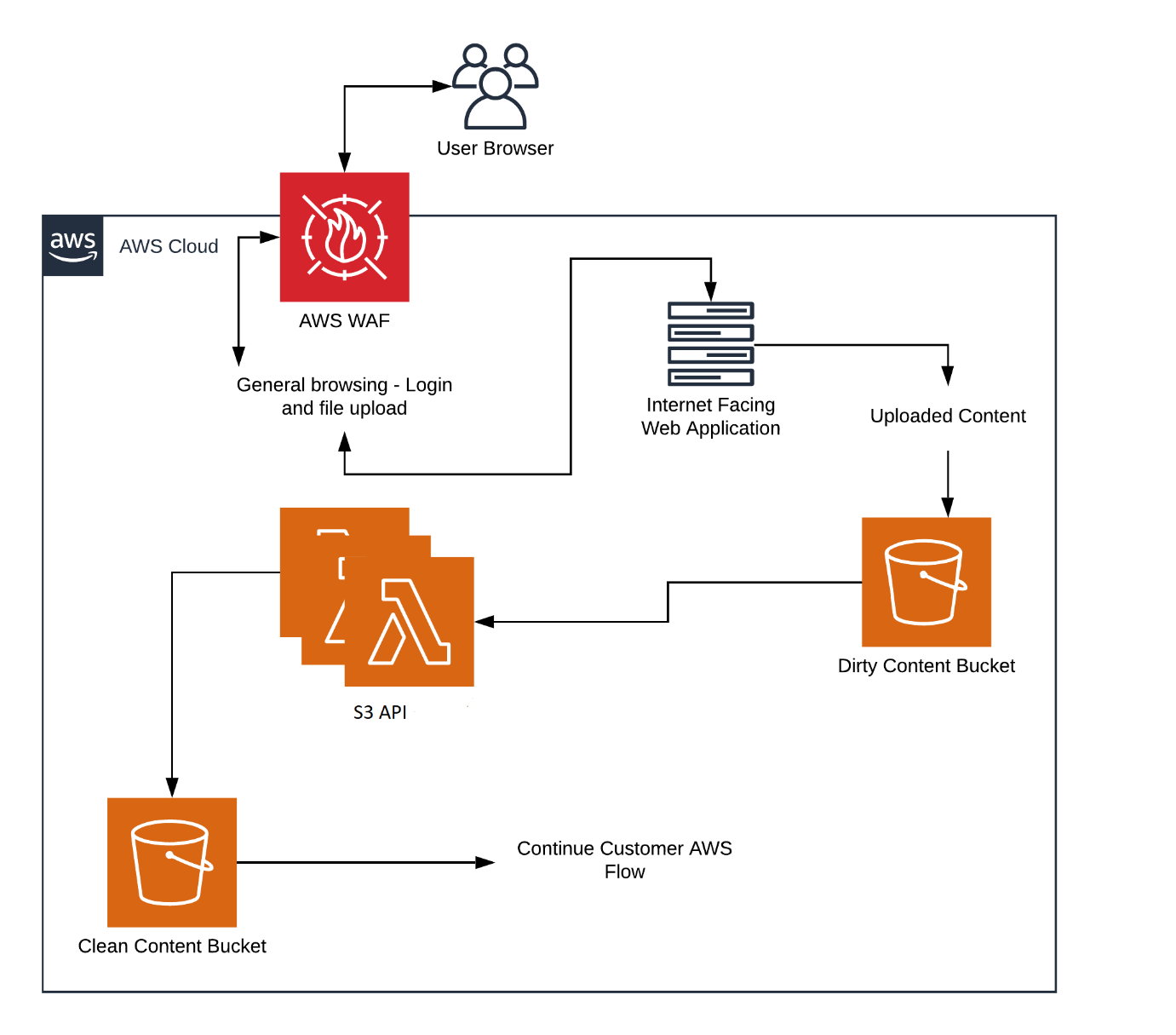
The example below is a high-level schematic showing how the Threat Removal S3 API can be used to protect an Internet-facing Web application from malicious file uploads. In this scenario, the entire application is resident in AWS with calls being made via the Threat Removal API to sanitise files as they move between “dirty” and “clean” storage buckets.
For More Information
See how Deep Secure Threat Removal APIs prevent malicious files from being uploaded into the Web applications responsible for a national government’s entire benefit system.
You can also discover how Deep Secure Threat Removal APIs are used in an application to protect an Internet-facing data warehouse for the American Land Title Association (ALTA).
Developers can get free access to the APIs for 30 days by visiting the developer portal where they can also download documentation, useful code fragments and see for themselves how to prevent malicious file uploads being used to attack cloud applications.


